
A botnet is a network of compromised computers that are used by hackers to launch DoS or DDoS attacks. This attack, done by using several hacked computers, is called a botnet attack.
According to a security brief in NZ 2024, botnet-driven Distributed Denial of Service (DDoS) attacks increased by 82%, rising from 90,000 incidents in 2023 to over 165,000 in 2024.
In this article, we will explain about botnets in cyber security, and the step-by-step process of botnet attacks. We will also discuss the preventive strategies you can adopt to protect your device from becoming part of a botnet.
Furthermore, if you are interested in getting into the cybersecurity field, you can check out our Cybersecurity courses.
What is a Botnet?
A botnet is a network of malware-infected devices that are controlled by a hacker, also called a bot herder, to carry out cyber attacks without the owner's knowledge or consent.
Individual devices in a botnet are called bots. They are managed through command and control (C2) servers by hackers for activities like DDoS attacks, data theft, and cryptocurrency mining.
Botnets in computer networks can also perform legitimate functions, like managing chat rooms or tracking game points, but they become dangerous when misused.

How do Hackers Create a Botnet?
Hackers create botnets by infecting multiple devices with malware that allows remote control. These devices can be your ordinary computers, servers, or IoT gadgets. They are silently turned into "bots" and linked together to form a network. Once assembled, the botnet can be used to launch large-scale attacks, steal data, or perform other malicious tasks without the users' knowledge.
Hackers use various techniques to infect devices and add them to a botnet. Some popular techniques are:
1. Phishing Emails: Trick users into clicking malicious links or downloading infected attachments.
2. Drive-by Downloads: Infect devices when users visit compromised or malicious websites.
3. Exploiting Software Vulnerabilities: Use known security flaws in outdated software to gain access.
4. Malvertising: Spread malware through fake or infected online ads.
5. Brute Force Attacks: Crack weak passwords to gain control of devices or servers.
What are Botnets Used For?
Botnets are used in:
● Distributed Denial of Service (DDoS) Attacks
● Spam and Phishing Campaigns
● Cryptocurrency Mining
● Spreading Malware
● Remote Control and Surveillance
Different Botnet Models
A botnet model defines how infected devices (bots) are controlled. There are different models of botnets based on the network’s efficiency, scalability, and stealth.
The three main botnet models are client/server, hierarchical, and peer-to-peer (P2P).
1. Client/Server Model
In this traditional setup, a central Command and Control (C&C) server directs all bots. It’s easy to manage but vulnerable, because if the server is taken down, the botnet collapses. There are two topology variations in this model:
● Star Topology: All bots connect to one central server, simple, but easily traceable.
● Multi-Server Topology: Uses multiple servers for redundancy and resilience.
2. Hierarchical Model
This model adds layers in bot management. A main server controls mid-level bots, which manage lower-level bots. It offers anonymity for the attacker, is scalable, and is resistant to partial shutdowns.
3. Peer-to-Peer (P2P) Model
In this decentralized design, every bot acts as both client and server. Bots exchange commands among themselves, making the network highly resilient with no central point of failure. It is hard to detect or dismantle.
What is a Botnet Attack?
A botnet attack is a type of cyberattack where a network of compromised computers(botnet) is used to carry out malicious activities. These attacks are very dangerous because a botnet can contain thousands or millions of infected devices, making it difficult to stop.
A single attacker controls the network of these devices and can remotely use these zombie computers without the consent of the actual owners. Hackers use botnets to use the computing power of multiple devices simultaneously.
Types of Botnet Attacks
Some common types of botnet attacks are:
| Attack Type | Description | Purpose |
|---|---|---|
| DDoS | Overwhelms a target with traffic | Disrupts services |
| Data Theft | Steals personal or financial information | Identity theft, fraud |
| Phishing/Spam | Sends malicious emails via infected bots | Spread malware, steal data |
| Crypto Mining | Uses devices to mine cryptocurrency secretly | Exploit resources, slow systems |
| Malware Distribution | Installs more malware on infected systems | Expand attack, deepen control |
| Click Fraud | Fake ad clicks to boost revenue | Defraud advertisers |
| MitM Attacks | Intercepts and alters user communications | Steal or manipulate data |
| DNS Hijacking | Redirects users to fake websites | Phishing, malware delivery |
How a Botnet Attack Works?
A botnet attack works by infecting as many computers as possible, maintaining access and control over them, so that they can be used in a cyber attack.
Here is a step-by-step process breakdown of a botnet attack:
Step 1: Target Identification
Hackers scan the internet for vulnerable devices such as computers, routers, or IoT gadgets with outdated software, weak passwords, or exposed ports that can be exploited..
Step 2: Infection
Once a target is found, malware is delivered through phishing emails, malicious websites, or software vulnerabilities. This malware silently installs itself and gives the attacker remote access to the device.
Step 3: Bot Enrollment
The infected device connects to a central Command-and-Control (C&C) server or a peer-to-peer network. It becomes a "bot," a remotely controlled unit in the botnet.
Step 4: Staying Hidden
The bot remains hidden, often using techniques like rootkits or encryption to avoid detection. It waits for commands while continuing normal device operations, so the user doesn’t notice anything unusual.
Step 5: Command Distribution
The botmaster sends instructions to the entire botnet or specific bots. These commands can include launching a DDoS attack, sending spam, mining cryptocurrency, or stealing data.
Step 6: Attack Execution
The bots carry out the commands simultaneously, leveraging their combined computing power. For example, in a DDoS attack, thousands of bots flood a server with traffic, causing it to crash.
Hackers regularly update malware, evade detection, and continue spreading the botnet to new devices to keep it active and growing.
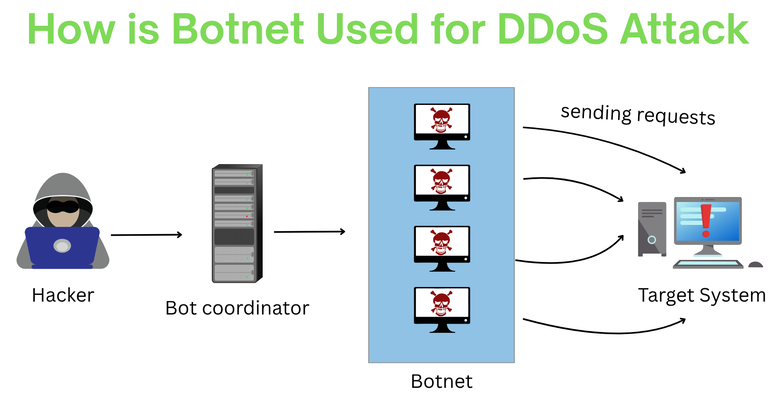
The image below shows how a hacker uses a botnet to carry out a DDoS attack on a platform.
Why Are Botnet Attacks So Dangerous?
A botnet attack is dangerous mainly because of its scale, stealth, and impact. Hackers control thousands and millions of infected computers to launch powerful cyber attacks like DDoS, which can shut down websites or services.
A botnet attack is very hard to trace because it comes from many sources, and since infected devices often appear normal, the attack can go unnoticed for a long time, making it even more harmful.
Botnets are very versatile and can be used for various cyber crimes like stealing data, sending spam emails, or spreading malware to increase botnet without users knowing. Their ability to cause widespread damage quickly makes botnet attacks a serious cybersecurity threat.
Examples of Botnets
Here are a few examples of popular botnets and the attacks they were used for.
1. Necurs Botnet (2017): This botnet was responsible for massive spam and phishing campaigns, impacting systems in India by spreading malware like Locky and Dridex.
2. Mirai Botnet (2016): Aimed at IoT devices, the Mirai botnet caused major DDoS attacks globally, affecting small businesses in India due to the hijacking of unsecured devices.
3. Andromeda Botnet (2017): Known for distributing a variety of malware, including ransomware and banking trojans, Andromeda also targeted users in India.
How to Know If Your Computer Is Part of a Botnet?
As we know, the owners of zombie computers in a botnet are unaware of it. But how can you find out if your system is compromised and is being used for malicious activities? Here are some signs that show your computer may be part of a botnet:
● Your system becomes sluggish or unresponsive without a clear reason.
● Internet usage spikes even when you're not actively browsing or downloading.
● Suspicious or unfamiliar applications appear in your task manager or startup list.
● Friends report receiving strange emails from your account.
● Your system crashes or shows error messages more often than usual.
How to Remove Your Computer from a Botnet?
If your computer is infected and is being used in a botnet, follow the given tips to recover from a botnet attack and gain control over it.
● Disconnect your PC from the internet by unplugging your network cable or disabling Wi-Fi to stop the botnet from communicating with your device.
● Restart your computer in Safe Mode to prevent malware from running during startup.
● Use a trusted antivirus or anti-malware tool (like Malwarebytes, Bitdefender, or Windows Defender) to detect and remove malicious software.
● Uninstall any unknown or suspicious applications from your system via Control Panel or Settings.
● You can reinstall a new OS or try updating the existing OS to patch any old vulnerabilities.
Tips to Protect Yourself From Becoming Part of a Botnet
1. Regularly install updates for your operating system, apps, and antivirus software to patch known vulnerabilities.
2. Use trusted antivirus and anti-malware tools that offer real-time protection and automatic scans.
3. Don’t click on unknown links or download files from untrusted sources, especially in emails or pop-ups.
4. Watch for signs like slow performance, high bandwidth usage, or unknown processes. These could be a sign of botnet activity.
5. Avoid default or weak passwords, especially for routers and IoT devices. Use a password manager to generate and store secure credentials.
6. Turn off features like remote access or open ports that aren’t needed, they can be entry points for attackers.
Conclusion
Botnets represent a serious and growing threat in the world of cybersecurity. By silently hijacking thousands of devices, attackers can launch powerful and disruptive attacks with minimal effort and high impact.
Understanding how botnets operate and recognizing the signs of infection is essential for individuals and organizations alike. With proper awareness, strong security practices, and timely action, it's possible to detect, prevent, and recover from botnet-related threats.

Amar Singh is a senior security architect and a certified trainer. He is currently working with a reputed organization based out of India. His accomplishments include CCNA, CCNP Security, CEH, Vmware, Checkpoint and Palo Alto Certifications. He is holding more than 12 years of experience in Network security domain. In his career he has been ...
More... | Author`s Bog | Book a MeetingFAQ
Comments (0)
Popular posts


What are the Different Types of Network ...
20 Jan 2026
What is the Syllabus for CCNA ...
20 Jan 2026
CCNA Exam Fees and Expenses Breakdown
25 Aug 2025
Transmission Media and Its Types in ...
20 Jan 2026Recent posts

What is the Syllabus for CCNA ...
20 Jan 2026
What is Switching and How Does it Work?
20 Jan 2026
Transmission Media and Its Types in ...
20 Jan 2026
What are the Different Types of Network ...
20 Jan 2026
What is a Hacker and How many types of ...
6 Jan 2026Upcoming batches
Contact learning advisor









