For more than ten years, cross-site scripting has been a regular member of the OWASP Top 10 web vulnerabilities. In the past, even major platforms like Twitter, Facebook, and Google have also faced cross-site scripting attacks.
This article aims to inform new developers and website owners about the cross-site scripting vulnerability, how it can be exploited for hacks, and what they can do to protect themselves from it.
Furthermore, if you want to be more informed about cyber security space, you can check out our cyber security courses and learn new ways to protect your online presence.
What is Cross-Site Scripting (XSS)?
Cross-site scripting (XSS) is a common web security vulnerability where hackers inject malicious scripts (usually JavaScript) into trusted websites. These scripts run automatically when users visit the compromised site, potentially exposing sensitive data.
These scripts are often added through URLs or user-generated content, such as comments or form inputs. When a user visits the affected page, the script runs automatically in their browser.
An XSS attack enables hackers to steal sensitive data, including cookies, session tokens, and login credentials. This happens because the browser trusts the site and executes the injected code as if it were safe.
These vulnerabilities usually occur when a web application fails to properly validate user input or encode output. Without proper sanitization, attackers can insert harmful code that gets executed by other users, putting their data and sessions at risk.
A cross-site scripting attack occurs when an attacker manages to insert harmful scripts, usually JavaScript, into web pages viewed by other users. These scripts can execute in the victim's browser, allowing attackers to steal cookies, session tokens, or other sensitive data.

What is Cross-Site Scripting Vulnerability?
A Cross-Site Scripting (XSS) vulnerability is a type of security flaw found in web applications that allows attackers to inject malicious scripts into content that other users will view.
A XSS vulnerability is usually found in user input fields such as search boxes, comment sections, or form inputs. If the application fails to properly validate or sanitize user input, these scripts can be executed in the browser of anyone who visits the affected page.
Developers can avoid and patch these XSS vulnerabilities by implementing strong input validation, using output encoding, and following secure coding practices. Using security headers like Content Security Policy (CSP) and frameworks that automatically escape user input can also help reduce the risk of exploitation.
How Does Cross-Site Scripting Work?
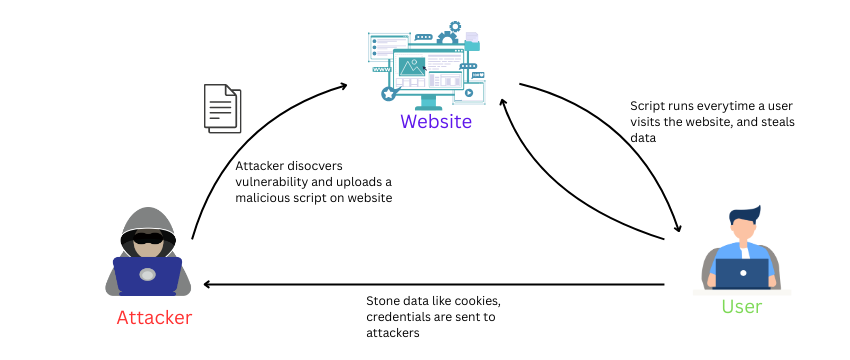
Here is a general process of a Cross-Site scripting attack.
1. Injection Point
The attacker finds a user input field like a search bar, comment box, or form that doesn't properly sanitize input. This becomes the entry point for injecting harmful scripts.
2. Malicious Payload
A malicious JavaScript payload is submitted through the vulnerable input. The script is designed to execute when a user views the resulting page, often without their knowledge.
3. Script Execution
When a victim loads the compromised page, the browser runs the malicious script as though it were part of the site's original code. This gives the attacker temporary control over that user's browser session.
4. Impact
Once executed, the script can steal session cookies, log keystrokes, redirect users to malicious websites, or perform unauthorized actions on their behalf.
Types of XSS Attacks
There are several types of XSS attacks, each with its own unique method of attacking:
1. Reflected XSS
Reflected XSS occurs when malicious scripts are embedded in a URL or HTTP request and immediately reflected in the response. It typically requires the victim to click a specially crafted link. This type of cross-site scripting attack is often used in phishing and social engineering schemes.
2. Stored XSS
Stored XSS involves injecting malicious scripts into a website’s database, such as in comment fields or user profiles. The script executes whenever users load the affected page. It poses a higher risk because it doesn't require user interaction with a crafted link.
3. DOM-Based XSS
DOM-based XSS is triggered by client-side scripts that manipulate the page's Document Object Model (DOM). The attack doesn't involve server-side processing and often uses data from the URL or user input. It's harder to detect and prevent since the payload executes entirely in the browser.
Dangers of Cross-Site Scripting (XSS)
Cross-site scripting (XSS) is a powerful tool for attackers aiming to exploit trust in a website to target users. It can be used to steal session cookies, capture login credentials, impersonate users, manipulate site content, and redirect victims to malicious websites.
XSS also enables attackers to spread malware or execute unauthorized actions on behalf of the user without their knowledge. When privileged users like administrators are targeted, the impact can escalate to full application compromise.
A notable real-world incident occurred in 2011 when eBay faced a persistent XSS vulnerability. Attackers were able to inject malicious JavaScript into product listings, which then executed in the browsers of anyone viewing the item. This flaw was used to redirect users to phishing pages that looked identical to eBay’s login page, allowing attackers to steal user credentials.
Despite the scale of the platform, the vulnerability persisted for some time and led to significant concern over eBay’s security practices. This incident highlights how XSS can be used not only to deceive users but also to damage the credibility of large, trusted platforms.
Why Fixing XSS Vulnerabilities Should Be a Top Priority
Cross-site scripting (XSS) is a critical web security issue that can severely impact users, applications, and businesses.
At the user level, XSS attacks can hijack sessions, steal credentials, and compromise privacy. Victims may unknowingly interact with fake login forms, click deceptive links, or even have malware silently installed through browser exploits.
At the application level, XSS can disrupt functionality, leak sensitive data, and deface websites. If admin accounts are targeted, attackers may gain access to confidential business or customer information. Stored XSS can even create persistent backdoors for future exploitation.
At the business level, the damage escalates. Organizations face financial losses, regulatory penalties, and reputational harm. A single XSS breach can erode customer trust, trigger legal consequences, and increase long-term security costs.
Fixing XSS vulnerabilities quickly is essential to protect users, maintain application integrity, and safeguard your brand.
How to Test for XSS Vulnerabilities
XSS vulnerabilities are best identified using a mix of automated tools and manual testing. Reflected, stored, and DOM-based XSS each require different approaches to find and exploit them effectively.
1. Automated Scanning
Tools like Burp Suite, OWASP ZAP, and Acunetix can automatically detect many XSS issues. These scanners crawl the application, analyze inputs, and test payloads to identify unsafe script execution. They’re efficient for initial assessments and large-scale applications.
2. Manual Testing
Manual testing starts by injecting unique strings into every user input and URL parameter. The goal is to see if the application reflects this data in its response without sanitization. Once located, you can test if JavaScript payloads execute, revealing an XSS flaw.
DOM-based XSS requires analyzing how JavaScript processes user input in the browser. Attackers insert test strings into the URL and observe how the DOM handles them. Tools like browser dev tools help trace how the data flows into unsafe functions like innerHTML or eval.
3. Testing Event-Based and Delayed Triggers
Some XSS attacks activate only during user actions like clicking or hovering. Others execute on timers or AJAX calls. Testing should include interacting with page elements and observing delayed script execution.
4. JavaScript Framework Considerations
Modern frameworks like Angular, React, and Vue may introduce framework-specific XSS risks. For example, Angular’s sandbox can be bypassed in some cases. Special attention is needed for properties like dangerouslySetInnerHTML in React.
5. Content-Type and Header Testing
Check how the application sets HTTP headers like Content-Type and X-Content-Type-Options. Misconfigurations can lead to browsers executing script content that should be treated as plain text.
6. Advanced Techniques and Tools
Advanced methods include testing for dangling markup injection and CSP (Content Security Policy) bypasses. These help detect XSS when full payloads are filtered. Source code review is also essential for spotting subtle DOM-based flaws.
Read this article about Best Cyber Security Tools
How to Prevent Cross-Site Scripting
Cross-site scripting prevention is vital for maintaining web application security. Key prevention strategies include:
● Input Validation: Ensure all user inputs are validated to allow only expected characters.
● Output Encoding: Escape special characters before displaying user data on web pages to prevent script execution.
● Content Security Policy (CSP): Implement CSP headers to restrict the sources from which scripts can be loaded.
● Use Security Libraries: Employ frameworks and libraries that automatically handle encoding and sanitization.
● Regular Security Testing: Conduct penetration testing to identify and remediate XSS vulnerabilities.
By combining these measures, organizations can significantly reduce the risk of XSS attacks.
Cross-Site Scripting vs SQL Injection
While both XSS and SQL injection are injection-based attacks, they target different layers of a web application. Cross-site scripting vs SQL injection differ in that:
| Feature | Cross-Site Scripting (XSS) | SQL Injection |
|---|---|---|
| Purpose | Targets users by executing malicious scripts in browsers | Targets databases by injecting malicious SQL code |
| Attack Surface | Client-side (browser) | Server-side (database) |
| Primary Language | JavaScript or other client-side scripts | SQL (Structured Query Language) |
| Target | User's session, cookies, browser data | Application database and data retrieval logic |
| Impact | Data theft, session hijacking, phishing | Unauthorized data access, data leakage, data loss |
| Detection | Harder to detect due to user-specific payloads | Easier to detect with proper input sanitization |
| Example Payload | <script>alert('XSS');</script> | ' OR '1'='1 |
| Defense Mechanisms | Output encoding, CSP, input validation | Prepared statements, parameterized queries |
| Common Entry Points | Forms, URLs, comment boxes | Login forms, query strings, API endpoints |
| Execution Location | Browser | Database server |
Read our detailed article on SQL Injection
Conclusion
Cross-site scripting (XSS) remains a major security threat due to its ability to hijack user sessions, deface websites, or spread malware. Awareness of XSS attack techniques, recognizing XSS vulnerabilities, and understanding different XSS types are crucial for developers and security teams.
Implementing strong cross-site scripting prevention practices ensures that web applications are safer and more resilient against these pervasive attacks.

Amar Singh is a senior security architect and a certified trainer. He is currently working with a reputed organization based out of India. His accomplishments include CCNA, CCNP Security, CEH, Vmware, Checkpoint and Palo Alto Certifications. He is holding more than 12 years of experience in Network security domain. In his career he has been ...
More... | Author`s Bog | Book a MeetingFAQ
Comments (0)
Popular posts


What are the Different Types of Network ...
20 Jan 2026
What is the Syllabus for CCNA ...
20 Jan 2026
CCNA Exam Fees and Expenses Breakdown
25 Aug 2025
Transmission Media and Its Types in ...
20 Jan 2026Recent posts

What is the Syllabus for CCNA ...
20 Jan 2026
What is Switching and How Does it Work?
20 Jan 2026
Transmission Media and Its Types in ...
20 Jan 2026
What are the Different Types of Network ...
20 Jan 2026
What is a Hacker and How many types of ...
6 Jan 2026Upcoming batches
Contact learning advisor