
BGP authentication is a crucial security feature within the Border Gateway Protocol (BGP) that ensures the integrity and authenticity of routing information exchanged between routers.
By implementing BGP authentication mechanisms, network administrators can prevent unauthorized devices from participating in BGP sessions, thus mitigating risks such as route hijacking and incorrect routing updates.
This process typically involves using techniques like MD5 hashing to secure BGP messages, ensuring that only trusted peers can exchange routing information. In this article, we learn how to configure BGP authentication on Cisco Routers.
It is an important concept in Cisco certification training and should be known by network enthusiasts looking to pursue any Cisco certification like CCNP.
BGP Authentication Methods
BGP uses TCP for transport, and because TCP already has a specification for authentication, BGP uses TCP authentication instead of a separate internal mechanism. Specifically, it uses TCP Option 19, which is the MD5 Signature Option.
There are two primary BGP authentication methods:
1. TCP MD5 Authentication
The primary method historically used for BGP authentication is the TCP MD5 Signature Option (RFC 2385). This approach involves generating a keyed hash using the MD5 algorithm, which is applied to TCP segments exchanged between BGP peers.
When configured, each BGP peer shares a secret key, and any received TCP segment must match the expected hash value to be accepted. If the authentication fails, the BGP session will not be established.
2. TCP Authentication Option (TCP-AO)
An enhancement to this method is the TCP Authentication Option (TCP-AO), introduced in RFC 5925. TCP-AO improves upon TCP MD5 by allowing for more robust authentication mechanisms and enabling key changes without disrupting existing sessions.
This option supports multiple Message Authentication Codes (MACs) and provides better protection against replay attacks, making it more secure than its predecessor.
Configuration Considerations
When configuring BGP authentication, it is crucial to ensure that both peers are using compatible methods (either TCP MD5 or TCP-AO) as they cannot be mixed on a single connection. Additionally, proper configuration of key chains and authentication algorithms is necessary to maintain secure and reliable BGP sessions.

How to Configure BGP Authentication
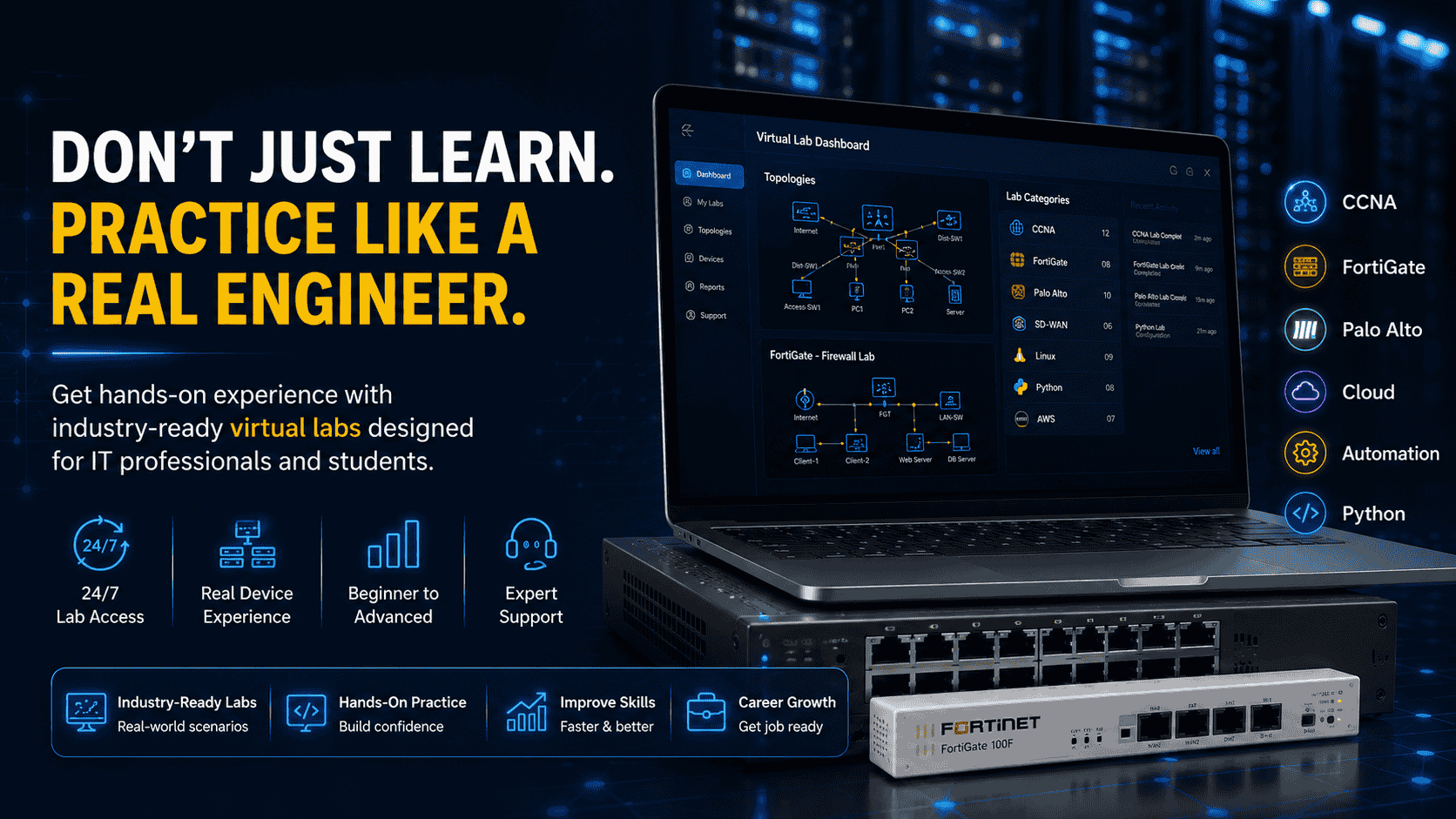
Let's look at the steps to configure and verify BGP authentication on Cisco routers. You can follow along with the tutorial on our virtual labs.
In this practical, we will complete some checkpoint tasks, to ensure step-by-step BGP authentication configuration.
Cisco BGP Authentication - Tasks
● Configure BGP on R01, R02, and R03 as per above topology.
● Use BGP ASN's 100, 200, and 300, respectively.
● Advertise the Loopback networks of the routers into BGP.
● R03 should peer with both R01 and R02.
● Configure BGP MD5 Authentication in these peering with the password UNINETS.
Here in this configuration, we are more focused on a scenario where both peers require BGP authentication and perform troubleshooting if required.
BGP Authentication and Other Configuration Commands
SW1:
R1:
R2:
R3:
Verify BGP Authentication Configuration
Just like in OSPF md5 authentication types, here also if BGP authentication fails, a peering relationship will not be established. Therefore, the most basic way to verify that BGP authentication is working is to look at the "show ip bgp summary" output and ensure that the peers are up.

The fact that prefixes are being received implies that the TCP session is up, but this could be further verified by viewing the BGP table, as seen below:
Outside of simply looking at the BGP configuration, authentication can be verified on a per-neighbor basis, as seen below:

A failure in BGP authentication will trigger a syslog message: Note- It may take a couple of minutes before these log messages appear.
Note that this is a different error message. If BGP authentication is simply not enabled on the peering, such as seen below: (You may have to reset the BGP neighborship to see these logs) though this is not recommended in the production environment.

This is an important difference that we will see later when BGP authenticated sessions pass through either the ASA firewall or the IPS sensor because the modifications they make to the IP header and payload will affect the TCP MD5 signature.
BGP Authentication & Configuration - Summing Up
BGP authentication enhances routing security by ensuring that only authorized peers exchange routing information. The primary method is MD5 authentication, which uses a shared password to generate an MD5 hash for TCP segments. Alternatively, the TCP Authentication Option (TCP-AO) offers improved security with multiple keys and key lifetimes.
To configure, enter BGP mode, set the neighbor with the password, and verify with "show ip bgp summary". Proper configuration ensures secure communication between BGP peers, protecting against unauthorized access and potential route hijacking.
To learn more about such technologies and networking concepts, check out our IT infrastructure courses.
Linkedin Profile: https://www.linkedin.com/in/uninets-deepak-sharma/ He is a senior solution network architect and currently working with one of the largest financial company. He has an impressive academic and training background. He has completed his B.Tech and MBA, which makes him both technically and managerial proficient. He has also ...
More... | Author`s Bog | Book a MeetingFAQ
Comments (2)

Hi Deepak, I read your blogs and most of them are with practical scenarios which are helping me to understand the concepts. Please keep doing this job. Thank you!!
Popular posts


What are the Different Types of Network ...
20 Jan 2026
What is the Syllabus for CCNA ...
20 Jan 2026
CCNA Exam Fees and Expenses Breakdown
25 Aug 2025
Transmission Media and Its Types in ...
20 Jan 2026Recent posts

What is the Syllabus for CCNA ...
20 Jan 2026
What is Switching and How Does it Work?
20 Jan 2026
Transmission Media and Its Types in ...
20 Jan 2026
What are the Different Types of Network ...
20 Jan 2026
What is a Hacker and How many types of ...
6 Jan 2026Upcoming batches
Contact learning advisor












It is a nice article, I prepared the same topology in GNS and BGP authentication between two peers are working. It is also right that error messages are different when password is not configured and wrong password is configured between bgp peers.
Full marks to the author.